Does it matter according to the Microsoft 70-686 dumps certification exam pattern? The Pro: Windows 7, Enterprise Desktop Administrator (70-686 Windows) exam is a 184 questions assessment in pass4itsure that is associated with the MCP certification. Best quality Microsoft 70-686 dumps study guide pdf Pro: Windows 7, Enterprise Desktop Administrator video study. “Pro: Windows 7, Enterprise Desktop Administrator” is the exam name of Pass4itsure Microsoft 70-686 dumps test which designed to help candidates prepare for and pass the Microsoft 70-686 exam. As I must consider Microsoft 70-686 test, I did recently been definitely freaking out since I truly doubted my own preparation. I we had not got considerable time prepare yourself possibly and that’s why the item came up as a surprise while I wound up passing https://www.pass4itsure.com/70-686.html dumps test along with flying colorings.
[New Microsoft 70-410 Dumps Release From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWemRUYmFFQVdJM1k
[New Microsoft 070-461 Dumps Release From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWRFNLVl8xNFJPejg
Pass4itsure Microsoft 70-686 Dumps Training Program Online Here(14-20)
Question No : 14 You use Group Policy to standardize Internet Explorer settings on Windows 7 client computers. Users occasionally change the Internet Explorer settings on individual client computers. What should you do?
A. Use Group Policy to disable the Advanced tab of the Internet Explorer Properties dialog box.
B. Use the Group Policy Update utility to refresh Group Policy.
C. Enable Internet Explorer Maintenance Policy Processing in Group Policy.
D. Enable User Group Policy loopback processing mode.
70-686 exam Answer: C
Explanation:
nternet Explorer Maintenance policy processing
This policy affects all policies that use the Internet Explorer Maintenance component of Group Policy, such as those in Windows Settings\Internet Explorer Maintenance. It overrides customized settings that the program implementing the Internet Explorer Maintenance policy set when it was installed. If you enable this policy, you can use the check boxes provided to change the options. Allow processing across a slow network connection updates the policies even when the update is being transmitted across a slow network connection, such as a telephone line. Updates across slow connections can cause significant delays. Do not apply during periodic background processing prevents the system from updating affected policies in the background while the computer is in use. Background updates can disrupt the user, cause a program to stop or operate abnormally, and, in rare cases, damage data. Process even if the Group Policy objects have not changed updates and reapplies the policies even if the policies have not changed. Many policy implementations specify that they are updated only when changed. However, you might want to update unchanged policies, such as reapplying a desired setting in case a user has changed it.
Question No : 15
Your companys network includes client computers that run Windows 7. You design a wireless network to use Extensible Authentication ProtocolCTransport Level Security (EAP-TLS). The Network Policy Server has a certificate installed. Client computers are unable to connect to the wireless access points. You need to enable client computers to connect to the wireless network. What should you do?
A. Install a certificate in the Trusted Root Certification Authorities certificate store.
B. Configure client computers to use Protected Extensible Authentication ProtocolCTransport Layer Security (PEAP-TLS).
C. Configure client computers to use Protected Extensible Authentication Protocol Microsoft Challenge Handshake Authentication Protocol version 2 (PEAP-MS-CHAP v2).
D. Install a certificate in the Third-Party Root Certification Authorities certificate store.
Answer: A
Explanation:
Question No : 16
Your company infrastructure includes a Windows Server 2008 R2 file server and 1,000 Windows 7 Enterprise client computers. The company wants to require a secure connection between client computers and the file server. You need to create and deploy a Group Policy object (GPO) that includes a rule for Windows Firewall with Advanced Security. What should you do?
A. Create an Isolation rule and specify Request authentication for inbound and outbound connections.
B. Create a Tunnel rule and specify Gateway-to-client as the tunnel type.
C. Create a Server-to-server rule and specify the endpoints as Any IP address and the file server IP address.
D. Create an Authentication exemption rule and add the file server IP address to the Exempt Computers list.
70-686 dumps Answer: C
Explanation:
The PDC emulator master also serves as the machine to which all domain controllers in the domain will synchronise their clocks. It, in turn, should be configured to synchronise to an external NTP time source
Question No : 17
You deploy Windows 7 to the computers that are used by your companys Web developers. All Web developer user accounts are in a single organizational unit (OU). Internet Explorer is blocking pop-up windows for multiple internal Web applications that are hosted on different servers. You need to use Group Policy to ensure that Internet Explorer does not block pop-up windows for internal Web applications. What should you do?
A. Enable Compatibility View in Internet Explorer.
B. Add each server to the Intranet zone.
C. Add each server to the Trusted Sites zone.
D. Set the default security setting in Internet Explorer to Medium.
Answer: B
Explanation:
Pop-up Blocker features
Pop-up Blocker is turned on by default. There are restrictions on the size and position of pop-up windows, regardless of the Pop-up Blocker setting. Pop-up windows cannot be opened larger than or outside the viewable desktop area. For more information, see “Windows Restrictions” in this document. When this functionality is enabled, automatic and background pop-up windows are blocked, but windows that are opened by a user click will still open in the usual manner. Note that sites in the Trusted Sites and Local Intranet zones do not have their pop-up windows blocked by default, as they are considered safe. This setting can be configured in the Security tab in Internet Options.
hints: internal web , so i choose intranet zones.
Local Intranet Zone
By default, the Local Intranet zone contains all network connections that were established
by using a Universal
Naming Convention (UNC) path, and Web sites that bypass the proxy server or have names that do not include periods (for example, http://local), as long as they are not assigned to either the Restricted Sites or Trusted Sites zone. The default security level for the Local Intranet zone is set to Medium (Internet Explorer 4) or Medium-low (Internet Explorer 5 and 6). Be aware that when you access a local area network (LAN) or an intranet share, or an intranet Web site by using an Internet Protocol (IP) address or by using a fully qualified domain name (FQDN), the share or Web site is identified as being in the Internet zone instead of in the Local intranet zone.
Trusted Sites Zone
This zone contains Web sites that you trust as safe (such as Web sites that are on your organization’s intranet or that come from established companies in whom you have confidence). When you add a Web site to the Trusted Sites zone, you believe that files you download or that you run from the Web site will not damage your computer or data. By default, there are no Web sites that are assigned to the Trusted Sites zone, and the security level is set to Low.
Question No : 18
Your network has client computers that run Windows 7 Enterprise. You plan to deploy new administrative template policy settings by using custom ADMX files. You create the custom ADMX files, and you save them on a network share. You start Group Policy Object Editor (GPO Editor). The custom ADMX files are not available in the Group Policy editing session. You need to ensure that the ADMX files are available to the GPO Editor. What should you do?
A. Copy the ADMX files to the % systemroot% \ inf folder on each Windows 7 computer, and then restart the GPO Editor.
B. Set the network share permissions to grant all Windows 7 users Read access for the share.
C. Copy the ADMX files to the %systemroot% \ system32 folder on each Windows 7 computer, and then restart the GPO Editor.
D. Copy the ADMX files to the central store, and then restart the GPO Editor.
70-686 pdf Answer: D
Explanation:
To take advantage of the benefits of .admx files, you must create a Central Store in the SYSVOL folder on a domain controller. The Central Store is a file location that is checked by the Group Policy tools. The Group Policy tools use any .admx files that are in the Central Store. The files that are in the Central Store are later replicated to all domain controllers in the domain.
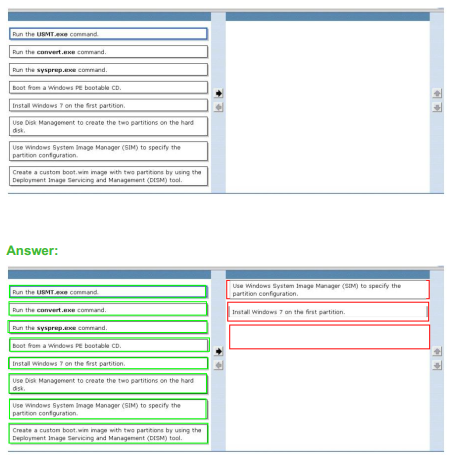
Question No : 19 DRAG DROP
You are planning to deploy Windows 7 Enterprise to all of your company’s client
computers.
You have the following requirements:
• Create two custom partitions on each client computer’s hard disk, one for the operating system and the other for data.
• Automatically create the partitions during Windows Setup.
You need to design an image that meets the requirements. Which two actions should you perform in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order)
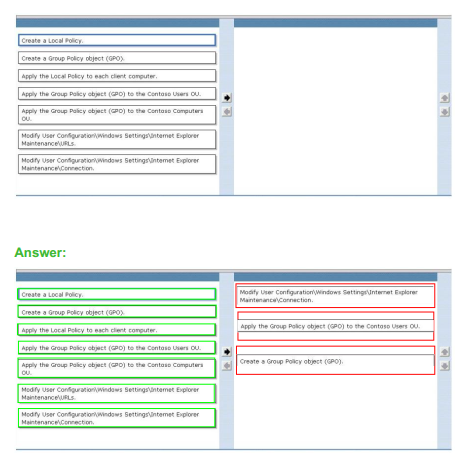
Question No : 20 DRAG DROP
All client computers in an organization run Windows 7 and are joined to an Active Directory Domain Services (AD DS) domain. All user objects are stored in an Organizational Unit (OU) named Contoso Users. All computer objects are stored in an OU named Contoso Computers. You need to add a proxy server to the Microsoft Internet Explorer 9 configuration on all client computers by using the least administrative effort. Which three actions should you perform? (To answer, move the appropriate action from the list of actions to the answer area and arrange them in the correct order.)
See What Our Customers Are Saying:
We at Pass4itsure are committed to our customer’s success. There are 50,000+ customers who used this preparation material for the preparation of various certification exams and this number of customers is enough for new candidates to trust in these products. Our products are created with utmost care and professionalism. We utilize the experience and knowledge of a team of industry professionals from leading organizations all over the world.
I must say which Pass4itsure is best intended for 70-686 dumps test as well as I solely get this to admission after presenting the situation some serious concern. “Pro: Windows 7, Enterprise Desktop Administrator”, also known as 70-686 exam, is a Microsoft certification which covers all the knowledge points of the real Microsoft exam. Pass4itsure Microsoft 70-686 dumps exam questions answers are updated (184 Q&As) are verified by experts. The associated certifications of https://www.pass4itsure.com/70-686.html dumps is MCP. To not boast too much or anything but I must say I always deserve to be which man intended for after in my life.
Compared with other brands, Pass4itsure has up to dated exam information, affordable price, instant exam PDF files downloaded, error correction, unlimited install,etc. Such as Pass4itsure Best Quality Microsoft 70-686 Dumps PDF, Real Microsoft 70-686 Dumps Self Study, We Help You Pass Pro: Windows 7, Enterprise Desktop Administrator. Simple and Easy! To take advantage of the guarantee, simply contact Customer Support, requesting the exam you would like to claim. Pass4itsure guarantee insures your success otherwise get your MONEYBACK!