Do you need Guaranteed Pass4itsure Q&A for the 70-483 dumps exam? The Programming in C# (70-483 Visual Studio) exam is a 242-question assessment in pass4itsure that is associated with the MCP, and MCSA certification.
Latest Microsoft 70-483 dumps Visual Studio exam questions actual 70-483 dumps Youtube training will be more popular. “Programming in C#” is the exam name of the Pass4itsure Microsoft 70-483 dumps test which is designed to help candidates prepare for and pass the Microsoft 070-483 exam. Microsoft https://www.pass4itsure.com/70-483.html dumps exam certification with the highest standards of professional and technical information, as the knowledge of experts and scholars to study and research purposes.
All of the products we provide have a part of the free trial before you buy to ensure that you fit with this set of data.
[New Microsoft 70-483 Dumps Release From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWQUM2eV9yZ2hMNTQ
[New Microsoft 070-464 Dumps Release From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWY000Mkw0VEZqYWM
Pass4itsure Microsoft 70-483 Dumps Training Program Online Here:
QUESTION 18:
You are creating a class named Employee. The class exposes a string property named EmployeeType. The following code segment defines the Employee class. (Line numbers are included for reference only.)
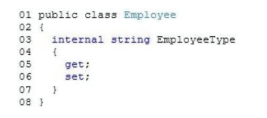
The EmployeeType property value must be accessed and modified only by code within the Employee class or a class derived from the Employee class. You need to ensure that the implementation of the EmployeeType property meets the requirements.
Which two actions should you perform? (Each correct answer represents part of the complete solution. Choose two.)
A. Replace line 05 with the following code segment: protected get;